
How to Optimize Windows Costs on AWS




How to Modernize Microsoft Workloads on AWS
Best Practices for Continuous Integration and Continuous Development



Why Machine Learning Projects Fail – and How to Make Sure They Don’t






ClearScale Squads: The Better Way to Manage Cloud Projects



8 Reasons to Migrate to the Cloud



Five Steps to Calculate AWS Cloud Migration Costs



5 Transformative Use Cases for AWS Cloud Migration



Why You Should Use Amazon RDS for Streamlining Your Database Management



4 Thoughts About GenAI and What Lies Ahead



5 Use Cases for Advanced Data Analytics Across Diverse Industries



Developing a Robust Data Strategy for Healthcare Organizations



Why Machine Learning Projects Fail – and How to Make Sure They Don’t



4 Thoughts About GenAI and What Lies Ahead


Most Commonly Asked Questions About GenAI



Key Security Considerations to Keep in Mind When Using GenAI
What is Amazon Bedrock?


From Neural Networks to Transformers: The Evolution of Machine Learning and the Future of AI Applications




6 Cloud-related Trends to Watch in 2024



An Overview of Amazon CodeWhisperer


Recapping Adam Selipsky’s AWS re:Invent 2023 Keynote Presentation


How ClearScale Streamlined Machine Learning Data Prep at American College of Radiology with Amazon SageMaker Low-Code / No-Code


What is Data Engineering and How Does it Relate to GenerativeAI?



What is Data Architecture and Why Does It Matter for GenerativeAI?
Best Practices for Continuous Integration and Continuous Development






ClearScale Squads: The Better Way to Manage Cloud Projects
Large-Scale Serverless Data Processing: 5 Best Practices



An Overview of Amazon CodeWhisperer



What is AWS Step Functions and How Does it Enable Event-driven Architectures?



Using the 12-Factor Approach for Microservices


What is Event-driven Architecture?



Database Modernization: Key Lessons Learned


Building Next-Gen Applications with Serverless Infrastructure


How Serverless Computing Works



4 Key Approaches to Kubernetes Cost Optimization


How to Develop Your Mainframe Modernization Strategy




How to Modernize Microsoft Workloads on AWS



8 Reasons to Migrate to the Cloud



Five Steps to Calculate AWS Cloud Migration Costs



5 Transformative Use Cases for AWS Cloud Migration




6 Cloud-related Trends to Watch in 2024


What to Expect at AWS re:Invent 2023



Accelerate Your Database Migration with the AWS Schema Conversion Tool


Build a Cloud Migration Business Case With the AWS Migration Evaluator



How to Migrate Legacy Databases to AWS


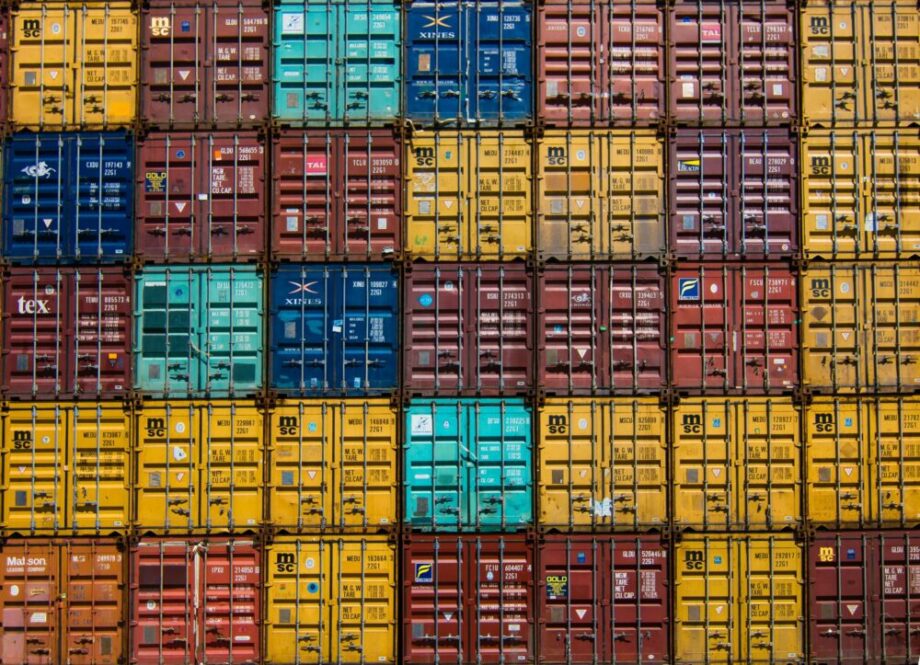
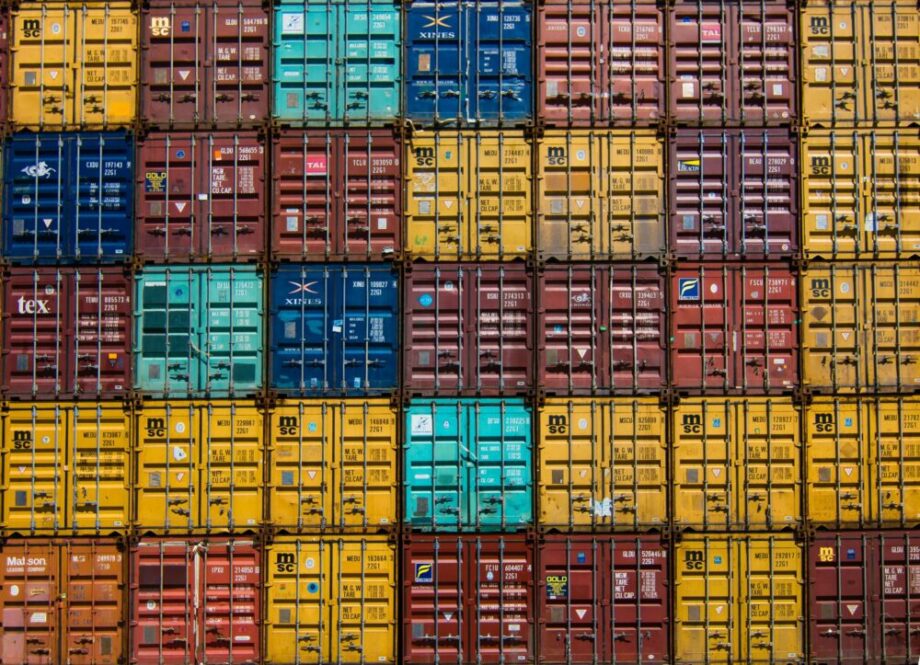
How the Cloud Enables Better Supply Chain Management


How the Cloud Impacts the Financial Services Industry


Revolutionizing Healthcare With the Cloud: AWS and Emerging Trends in HealthTech



How to Keep Your Kubernetes Deployments and Containers Secure with Amazon EKS


5 Key Approaches to Cost Optimization on Amazon ECS and AWS Fargate



4 Key Approaches to Kubernetes Cost Optimization



How to Be Successful with Multi-cloud and Hybrid Cloud Setups


What are the Benefits of Using Containers?


Microservices Observability


What Are Containers?
How to Implement Logging and Tracing for Containers


20 Kubernetes Best Practices and Recommendations


Container Orchestration: ECS vs EKS


Considerations for Choosing Serverless, Containers or Both
Container Security Risks and Remedies






ClearScale Squads: The Better Way to Manage Cloud Projects



5 Use Cases for Advanced Data Analytics Across Diverse Industries



Developing a Robust Data Strategy for Healthcare Organizations



What is Data Architecture and Why Does It Matter for GenerativeAI?


Unlocking Real-time Search with OpenSearch
Amazon DataZone and the Rise of Data Mesh
Is Your Data Ready for Generative AI?


6 Big Data Challenges and How AWS Can Overcome Them


Revolutionizing HealthTech: ClearScale’s AWS-based Data Lake Solution for Enhanced Scalability and Flexibility
An Overview of Data Ingestion Pipelines


The Five Elements of Cloud Data Lake Deployments


AWS Analytics Services: The Key to Big Data Success



Why You Should Use Amazon RDS for Streamlining Your Database Management


What are Cloud Databases?



Accelerate Your Database Migration with the AWS Schema Conversion Tool



How to Migrate Legacy Databases to AWS


Slash Costs and Boost Performance: Master Your Oracle to Aurora PostgreSQL Migration Journey



Database Modernization: Key Lessons Learned


An 8 Step Process for Database Migration to AWS PostgreSQL
5 Common Database Modernization Myths


Migrating From Cassandra to DynamoDB: The Whys and Hows


It’s Time to Migrate Your Legacy Databases to the Cloud


AWS Managed Database Services - What’s New at re:Invent 2020
Cloud Databases 101: Introduction to Amazon Aurora
Best Practices for Continuous Integration and Continuous Development






ClearScale Squads: The Better Way to Manage Cloud Projects


Horizontal vs. Vertical Scaling: What’s the Difference?


What is Cloud Infrastructure Management?



What is AWS Step Functions and How Does it Enable Event-driven Architectures?


What are Cloud Optimization Services?



Using the 12-Factor Approach for Microservices


Cloud Landing Zones: What Are They and Why Do They Matter?



How to Be Successful with Multi-cloud and Hybrid Cloud Setups


AWS Step Functions vs AWS Lambda


CI/CD Best Practices for Overcoming Cloud-native App Challenges


10 Best Practices for Cloud-native Application Development


Bringing IoT to the Edge: How Edge Computing is Transforming Data Analysis on the Cloud


IoT App Development - The AWS Way



A Guide to the AWS Well-Architected Framework - Building Your Cloud Foundation


Recapping Adam Selipsky’s AWS re:Invent 2021 Keynote Presentation


Top 4 Benefits of IoT Applications in the Cloud


5 Must-Use AWS Services for IoT Applications


Accelerating Time-To-Market for Smart Industrial IoT Applications


Overcoming IoT Disaster Recovery Limitations Using Multiple AWS Regions
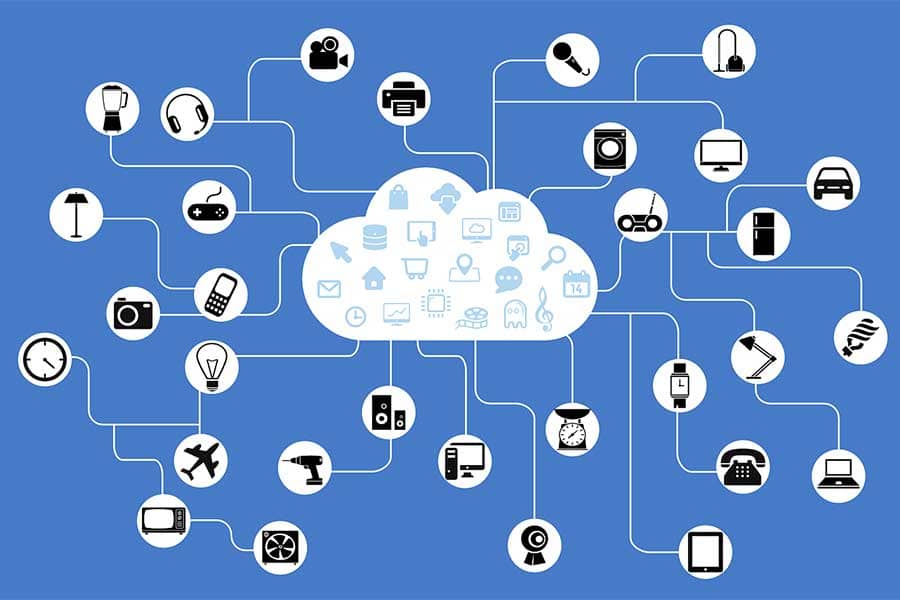
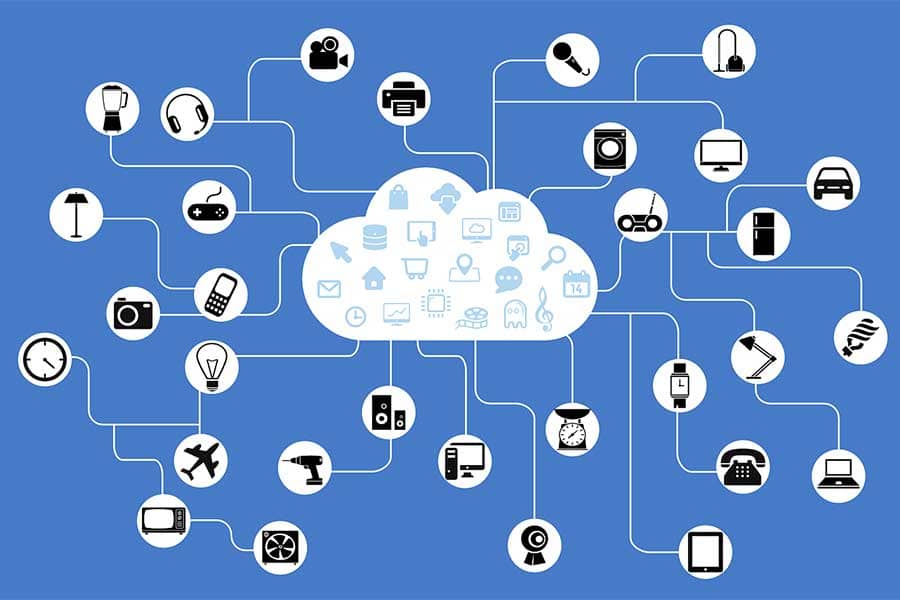
Implementing an Internet of Things (IoT) Solution and Building a Device Emulator on AWS Platform






ClearScale Squads: The Better Way to Manage Cloud Projects


Cloud Managed Services Provider vs. DIY: 5 Considerations



ClearScale Wins Best Innovative Project in Channel Partner Insight’s MSP Innovation Awards


How to Choose The Right IT Services Firm for a Post COVID World


Managed DevOps: Why It’s Needed. Where to Get It.


How the Cloud Has Affected the SaaS Industry


For SaaS Development, AWS is the Best Choice



A Guide to the AWS Well-Architected Framework - Building Your Cloud Foundation


Why ISVs and SaaS Vendors Should Go Cloud Native with AWS and ClearScale



ClearScale Earns SaaS and Education Competencies from AWS


Monolithic App to Microservice Transformation


Fully Automated SaaS Solution Powered by Marathon, Mesos, Chef, and Docker



Key Security Considerations to Keep in Mind When Using GenAI




6 Cloud-related Trends to Watch in 2024



How to Keep Your Kubernetes Deployments and Containers Secure with Amazon EKS


10 Essential Security Tools for Your AWS Environment
How the Cloud Makes Fraud Detection Easier


What is the Shared Responsibility Model?


Recapping Adam Selipsky’s AWS re:Invent 2022 Keynote Presentation


AWS SIEM Solutions from ClearScale
Why You Need Managed Services and Monitoring for the AWS Cloud


The Case for Managed Security Services


Overcoming Remote Work Security Challenges with AWS


AWS Implementation Project Plan Takes Flight with AWS Control Tower and AWS Landing Zone



How to Optimize Windows Costs on AWS




How to Modernize Microsoft Workloads on AWS


5 Key Benefits of Moving Windows Workloads to AWS


Migrating and Modernizing Windows Workloads on AWS


Migrating Windows Workloads to AWS Generates Savings


Moving Ahead with Application Modernization


Segregated Environments and DevOps Ensure High Availability and Security for Web Apps


Reasons to Migrate and Modernize Windows Workloads with AWS
